- Content Management System Software
- Point of Sale Software
- Fleet Management Software
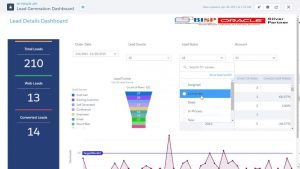
- CRM Software
- Contract Management Software
- Mind Mapping Software
- eCommerce Software
- CMS Software
- Backup Software
- EMR Systems
- Construction Management Software
- Contact Management Software
- Document Management Software
- Collaboration Software
- Marketing Software
- Business Management Software
- CAD Software
- HR Software
- Accounting Software
- Customer Support Software
- Project Management Software
- Learning Management System
- Property Management Software
- Business Intelligence Software
- Sales Software
- Help Desk Software
SHOW ALL CATEGORIES